Please Take Note: This is a review of the final game, but it might change slightly based on the success of the Kickstarter campaign. The game is being reviewed on the components and the rules provided with the understanding that “what you see is not what you might get” when the game is published. If you like what you read and want to learn more, we encourage you to visit the game’s website or visit the Kickstarter campaign. Now that we have all that disclaimer junk out of the way, on with the review!

The Basics:
- For ages 6 and up (publisher suggests 7+)
- For 2 to 4 players
- Approximately 10 minutes to complete
Geek Skills:
- Counting & Math
- Logical & Critical Decision Making
- Pattern/Color Matching
- Strategy & Tactics
- Risk vs. Reward
- Hand/Resource Management
- Area Control
Learning Curve:
- Child – Easy
- Adult – Easy
Theme & Narrative:
- Boot your computer and compile your code in hopes of being the first hacker to bust into an unbreakable mainframe
Endorsements:
- Gamer Geek approved!
- Parent Geek approved!
- Child Geek approved!
Overview
According to the chatter on the forums and the annoying posts from script kiddies, a computer mainframe went online that was supposedly unhackable. Impossible! Even the toughest armor has a seam that can be exploited. You decide that you are going to make hacker history and be the first to punch a hole in the most secure mainframe to date. Of course, others have the same idea. Let the race begin! Hackers, start your decryption programs!
Firewall, designed by Jonathan King, Sean Steele, and to be published by Sarcastic Robot, will reportedly be comprised of 1 game board and 40 custom six-sided dice (in 4 different colors, 10 dice per player). As this is a review of a prepublished game, we will not comment on the game component quality. Nor can we suggest that the stated game components will be the only ones included in the game box. Additional components might be included with the game based on the success of the Kickstarter campaign and any overfunding goals achieved. Not included with the game, but nice to have, is a pen or pencil and a piece of paper to keep track of the player’s victories. A single game of Firewall take very little time to complete. Several games in a row can be played to determine the overall winner well within the span of 1 hour.
Hacker Basics
Firewall uses a number of computer science terms, but understanding how computers work is not necessary to play the game.
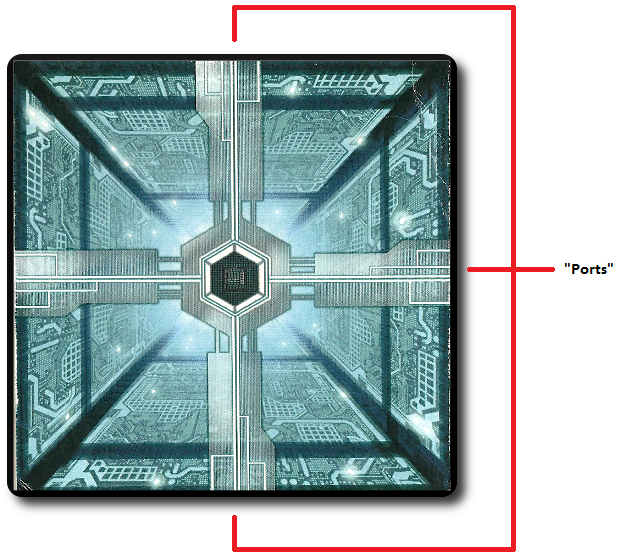
Ports and Data Streams
The game board represents the computer mainframe the players are attempting to hack into. The mainframe has a total of 4 “Ports” (one Port on each side of the square game board). It’s here players will be placing dice. Each Port contains 1 “Data Stream”. A Data Stream is a row of dice attached to a Port that represents the input from the players.
Storage
A player’s “Storage” is their pool of dice they have access to, but have not yet used. Every player starts with 10 dice in their Storage dice pool. From their Storage, players will be collecting dice to use on their turn, but the total number of dice available will quickly be reduced.
RAM
A player’s “RAM” allows them to save 1 die roll. This is a previously rolled die from the player’s Storage dice pool, but the value rolled is locked and set aside. It cannot be rolled again until the die returns to the Storage dice pool, but it can be played instead of one of the dice values rolled on a player’s turn. Only 1 die at a time can be saved in a player’s RAM, but it can be replaced by another die value.
Bootup
To set up the game, first give each player 10 dice of a single color. Any dice not used are removed for the duration of the game.
Second, place the game board in the center of the playing area and within easy reach of all the players.
Third, one player rolls 1 of their die and continues to roll the same die until they get a number result. The number rolled will determine how many Ports the players will be using during the game.
- 1 “Program” = 2 “Ports”
- 2 “Programs” = 3 “Ports”
- 3 “Programs” = 4 “Ports”
Fourth, each player then rolls 5 of their dice to determine who will go first. The player who rolls the most Firewalls is the first player. Ties are broken on the number of Programs rolled, with the tie going to the player who has the most Firewalls and Programs.
That’s it for game set up. Time to show the hacker world how 1337 you are.
Breaking the Firewall
Firewall is played in turns with no set number of turns per game. On a player’s turn, they will complete the following steps.
Step 1: Roll
The player takes 3 dice from their Storage dice pool and rolls them. If the player has less than 3 dice left, they roll whatever dice remain. From the dice values rolled, the player selects 1 die to play. The remaining die are returned to the player’s Storage dice pool or 1 of the die can be swapped with the die in the player’s RAM or simply added to RAM it if no die has been assigned to it yet. A player can also elect to use the die value in their RAM if they are not satisfied with what they rolled.
Step 2: Control
The player places their selected die in a row that branches off from one of the 4 Ports. The row of dice emerging from a Port is referred to as a Data Stream. Remember: the number of Ports the players can use during a single game was determined during the game set up. If the players are only allowed to use 3 Ports, for example, they cannot place a die on a fourth Port. All Ports are the same and there is no advantage to selecting one Port versus another on the game board when starting a new Data Stream.
What each die value does and represents is summarized here.
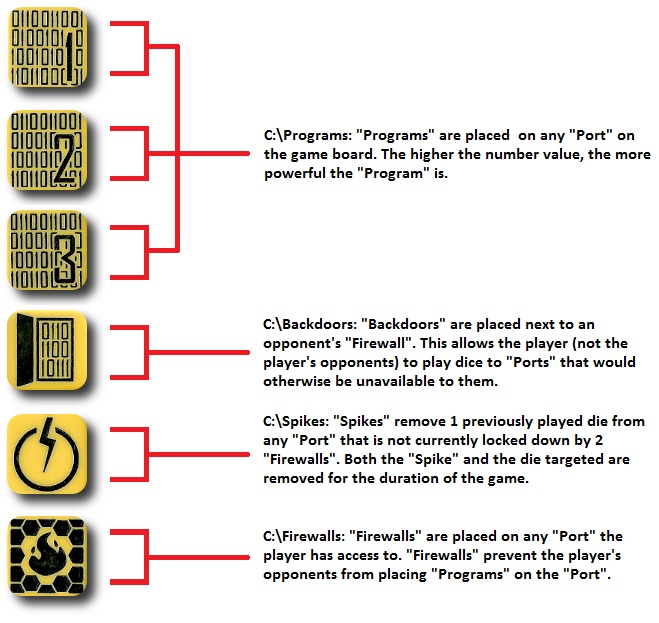
A few additional notes regarding the dice and how they influence Data Streams.
- Programs count towards a player’s overall control of a specific Port. As such, a single Data Stream could contain multiple Programs from multiple players. There is no limit to the number of Programs a single Data Stream can contain.
- Firewalls lock out a player’s opponents from the Data Stream. Two Firewalls of the same color on a Data Stream locks out all players. A single Data Stream could contain multiple Firewalls from different players. If a player wants to add dice to a Data Stream that has an opponent’s Firewall on it, they must have a Backdoor attached to their opponent’s Firewall. In this way, a player could have multiple Backdoors on a single Data Stream.
- Backdoors are placed next to an opponent’s Firewall located on a Data Stream. The player can now add dice to the Data Stream as normal. A new Backdoor is necessary every time an opponent plays a Firewall to a Data Stream if the player wants to add dice to it. Multiple Backdoors can be attached to a single Firewall.
- Spikes remove a single die in the Data Stream. Both the Spike and the removed die are out for the duration of the game. When a die is removed, all the dice in the Data Stream adjust their position by moving towards the center of the game board. In this way, gaps are filled in the Data Stream which is always made up of a continuous row of dice. Any Backdoors attached to Firewalls move with the Firewall. If a Firewall is Spiked with an attached Backdoor, both the Firewall and the Backdoor are removed. Spikes can be played on any Port and any Data Stream, even those that have locked a player out due to a Firewall with no player-owned Backdoor attached. The only restriction for a Spike is that they cannot be played on a Port that has been completely locked down by 2 Firewalls of the same color in the Data Stream.
Once the die is placed or played, the player’s turn is over and the next player in turn order sequence takes their turn starting with step 1 noted above. Any unused dice are returned to the player’s Storage dice pool. Any die in RAM retains its rolled value.
Random Access Memory (Die)
The choices available to the player are determined by the random die results, but a smart hacker always has a trick in their back pocket. Every player has a reserved space in front of them referred to as the player’s RAM. Unlike the player’s Storage dice pool that only provides random die results, the player’s RAM can contain 1 die value indefinitely until such time the player must play a die and the only one left is the one located in their RAM.
Players can roll their 3 dice as normal on their turn and then decide if they want to used any of the rolled results or use the die in their RAM. If they do decide to use the RAM die, they can take any 1 of their rolled die values and place it in their now empty RAM space. Likewise, a player can always replace any die in their RAM with a rolled die value, regardless if they use the RAM die or not. If the die in RAM is replaced with another die value, it is returned to the player’s Storage dice pool.
H4X0R3D!!!
The game continues as described above until all the players have played their dice to the Ports or all the available Ports are locked down with 2 Firewalls of the same color in each of the Data Streams. All the players now review the game board and determine which player controls the majority of Ports.
To determine who controls a Port, count the number values of all the Programs located in the Data Stream. The player with the most points derived from the Program dice controls the Port. If there is a tie for a specific Port, the total number of Program dice is used to break the tie.
The player who controls the most Ports has hacked the mainframe and wins the game.
To learn more about Firewall and read the full rules, visit the game’s website or visit the Kickstarter campaign.
Prediction
Dice games continue to be a big hit with our groups and I have no doubt that Firewall will meet with great success for several reasons. First, the game is competitive and you have the ability to skunk your opponents. That will appeal to the Gamer Geeks. Second, the game does require tactics and strategy, albeit light on both accounts. Players must always be looking for an opportunity to get the upper hand and lock out their opponents. Timing is going to be essential to obtain victory, although luck is still part of the game play. Third, the players always have a choice, despite the dice values always being random. This is especially true if the player saves a die value to their RAM. For example, a much-needed Backdoor or a second Firewall to lock down a Port for the win. Players can use a saved die to mitigate the randomness of dice rolls and reduce their dependency on luck. Fourth, and finally, the game is very easy to learn and quick to play. The game has depth and will require its players to think, but nothing about the game suggests that it will be difficult to grasp or to enjoy.
Teaching Firewall is going to take only about 2 to 3 minutes. Just roll 10 dice and show how they connect and work. Make sure you explain that a player will need a Backdoor for every Firewall played by an opponent if they want to contribute to a Data Stream. Other than that, just make certain all the players understand how a Spike can be used, even if the player no longer has access or zero influence in a specific Data Steam. Most of the questions we were asked focused on RAM. The current rules are a bit light on specifics, but there is enough detail to understand how it can and should be used. Once those questions were answered, all of our players were ready to go.
There were also a few players who were concerned that they would be at a disadvantage because they knew next to nothing about computers. Again, a player need not know ANYTHING about computers to play Firewall. Computers, hacking, and programs are just part of the theme, but understanding those terms is not necessary to be competitive. At most, a player who does not understand the terms might not feel as engrossed in the game’s subtle narrative.
After teaching Firewall to my two oldest little geeks, I asked them their thoughts on the game so far.
“Super cool! I like how we get to play hackers and break into a big computer!” ~ Liam (age 9)
“I like it, Daddy. It’s not a hard game for me to play!” ~ Nyhus (age 6)
The theme of the game is a bit beyond my 6-year-old to grasp, but my 9-year-old (who is very interested in Netrunner) really digs it. Again, you don’t need to understand how to use a computer or even know what a computer looks like to play Firewall. My 6-year-old is not at a disadvantage whatsoever. This is a game about rolling dice and making informed decisions.
Let’s play Firewall and see if we have fun or get burnt.
Final Word
The Child Geeks had a great time with Firewall and played it beautifully. The older Child Geeks demonstrated a higher level of critical and logical thinking when it came time to make choices, but the younger Child Geeks made solid moves. It all came down to the individual player’s personality. The more aggressive players locked out their opponents as soon as possible, while the more passive players worked around Firewalls and did their best to make as many points as possible before the game ended. Both strategies worked well together. According to one Child Geek, “What I really like about this game is that I feel like I am a hacker making my way into a really big computer!” Another Child Geek said, “I like this game because what I need to do always makes sense.” All the Child Geeks really enjoyed the speed of the game and how involved they had to be to play it. Rolling dice always gave them something new to think about and something new to work with. When the game was put away, all the Child Geeks voted to approve Firewall.

My little geek smirks, as his dice roll results in a much-needed Firewall to lock me out! Nooooooooos!
The Parent Geeks enjoyed Firewall at the family gaming table and with their peers. A number of the non-gamer and less experienced Parent Geeks were surprised how quickly they “got the game” and how much fun it was to play. According to one Parent Geek, “I was concerned about this game because it was about hacking and computers, but I never once was confused.” All the Parent Geeks enjoyed the pace of the game and how casual it was. They played several games in a span of 30 minutes and were ready for more after the last point was counted. When the game was put away, all the Parent Geeks voted to approve Firewall, finding it to be a fun and fast game that was enjoyed by everyone at the table.
The Gamer Geeks were immediately intrigued by the idea of the game. Netrunner is pretty big right now in many gaming circles and the hacker cyber punk theme and narrative that exists in many role-playing, card, and board games always draws a crowd. When they found out that Firewall was a dice game, they were skeptical. “Dice” often times means “randomness”. If there is one thing Gamer Geeks dislike, it’s a game that is too random. You can’t take actions in a game setting that is always shifting. The best you can hope for is reacting correctly, which doesn’t allow for much in the way of strategy or tactics. Luck plays a huge part in games that are too random and not many Gamer Geeks like games where the winner is determined by random elements or events.
The Gamer Geeks were very pleased to learn that they always had multiple choices. Rolling 3 dice instead of 1 could provide up to 3 different options and the ability to save a die in RAM always provided players with a known value. According to one Gamer Geek, “This is a perfect game to play as a filler, before an evening of larger games, or as the very last game of the evening. I really like it.” And while all the Gamer Geeks agreed that Firewall was fun, a few of the Gamer Geeks thought it was also somewhat flawed. According to one of these Gamer Geeks, “I still think there’s a bit too much randomness and bit too much luck for my personal taste, but I really don’t like how the number of Ports in every game is randomly determined. I’d rather there always be just 1 Port per player and call it good.” And yet another Gamer Geek said, “The game can get a bit repetitive, but the speed of the game keeps it light and super easy to tolerate.” When the game was put away and it came time to vote, all the Gamer Geeks agreed Firewall was either a “really good casual game” or “just good enough to keep them interested.” In short, it was approved.
Despite only having Firewall for a couple of weeks, I’m a huge fan of the game. I play a lot of Dice games with my little geeks and that is, frankly speaking, getting old. Their current favorites are Martian Dice and Zombie Dice. Great games for the little geeks and excellent for when there isn’t a lot of time, but they don’t let players interact. With no player interaction, you are forced to simply watch until it’s your turn again. That can be pretty boring. Firewall was a real treat as it provided all the tactile fun of a Dice game with a real need to think through each of my moves and be mindful of other players. But it was the speed in which the game could be played and completed that really tickled me. I could play several games in a row and not once did my mind register the downtime between turns. I enjoyed every roll, regardless if it resulted in sweet victory or bitter defeat.
Would I recommend Firewall? Without question. It’s a great Dice game that was enjoyed by all who played it. Not everyone loved it, but no one walked away from the table feeling like they wasted their time. And when you consider that a normal series of games will take you less than 30 minutes, Firewall is one of those games you can fit into your schedule easily. It demands little, is fun to play, and is quick to complete. Do take a look at Firewall. If you are a fan of Dice games, you are most certainly going to enjoy it.
This is a paid for review of the game’s final prototype. Although our time and focus was financially compensated, our words are our own. We’d need at least 10 million dollars before we started saying what other people wanted. Such is the statuesque and legendary integrity of Father Geek which cannot be bought except by those who own their own private islands and small countries.
Discover more from Father Geek
Subscribe to get the latest posts sent to your email.



Great review. This is so very tempting, but the price seems out-of-whack to me. One copy of the game on Kickstarter is $31 (MSRP $35). That’s $31 for 40 dice and a square of cardboard. I realize the dice are custom, but it seems like comparable games are much cheaper. For instance, here are similar quick dice games and their prices:
Dungeon Roll – $20 MSRP
Martian Dice – $15 MSRP
Zombie Dice – $14 MSRP
Dungeon Dice, containing 80+ custom dice – $45 on Kickstarter
Quarriors, containing 130 custom dice – $60 MSRP (~$40 online)
Based on the components and playtime, I would have happily paid $20-25 for a set of Firewall. Are my expectations out of line? Is it worth the higher than expected cost?
Thanks for taking the time to read and leave a comment, Mr. Titelbaum.
Yes, I would agree that the price you are paying for the game via Kickstarter is higher than expected. I physically winced when I read the pledge goal and tier levels. This is further reinforced by your findings that compare the current price of Firewall to other custom dice games available today.
Making games is not cheap and shipping from overseas costs more than an arm and a leg. Perhaps the amount being asked for is based on the growing cost to publish a game in today’s market? We must also consider that the company is making 8 different sets of custom dice in the colors red, green, blue, white, cyan, magenta, yellow, and black. That can’t be cheap.
I can confirm for Cyrus. Having custom dice is 8 colors does make it more expensive. The reason we are making 2 versions of the game is so you can combine the to make play with 8.
I appreciate you’re input Matthew, and I can understand for a short game that $35 seems expensive. That’s because of the 40 high quality custom dice, featuring a complex design. I wanted to keep Firewall under $40 because it’s not a big box game like Catan. I felt like $35 seemed like a much fairer price and I think the game has the potential and replayability to return on that investment.
Dungeon Roll – $20 MSRP – 13 dice and a horde of components. MSRP/dice = $1.53
Martian Dice – $15 MSRP – 13 dice, and just the dice. MSRP/dice = $1.15
Zombie Dice – $14 MSRP – 13 dice, and just the dice. MSRP/dice = $1.07
Dungeon Dice – $45 on Kickstarter – containing 80+ custom dice. MSRP/dice $.56 – I want to point out the designs are much simpler and in one color.
Quarriors – $60 MSRP – 130 dice – MSRP/dice = $.46 – This game is from wizkids. I’m a small time publisher so I can’t compete with their economy of scale.
Based on what you pay for martian dice Firewall should be $46 MSRP. I’m offering it on kickstarter for $31.
Don’t quickly discard the board either. That’s why we can’t put the game in a tin, and it costs money itself. I was trying not to go cheap on components but rather have something you’d like to look at while you were playing.
I hope that explains the pricing a little better.
-Jonathan King
Sarcastic Robot